Author: chris
-
Comments on Sustainability, Round 2
Thank you for the opportunity to comment on the proposed revisions to the University of California Policy on Sustainable Practices. I share the University’s commitment to environmental stewardship. My comments focus not on the aspirations of the policy, but on questions of scope, prioritization, cost, and institutional capacity, issues that I believe warrant fuller consideration…
-
Norms as Ontologies: Berkeley’s Virtue Signaling with Externalization
One of the things I treasure most about Berkeley is the sincerity of its community. As a public university, Berkeley aspires not merely to produce knowledge but to foster civic virtue. Our official statements are filled with values I share: equality, stewardship for the environment, belonging, accessibility, justice. These are noble commitments. They form part…
-
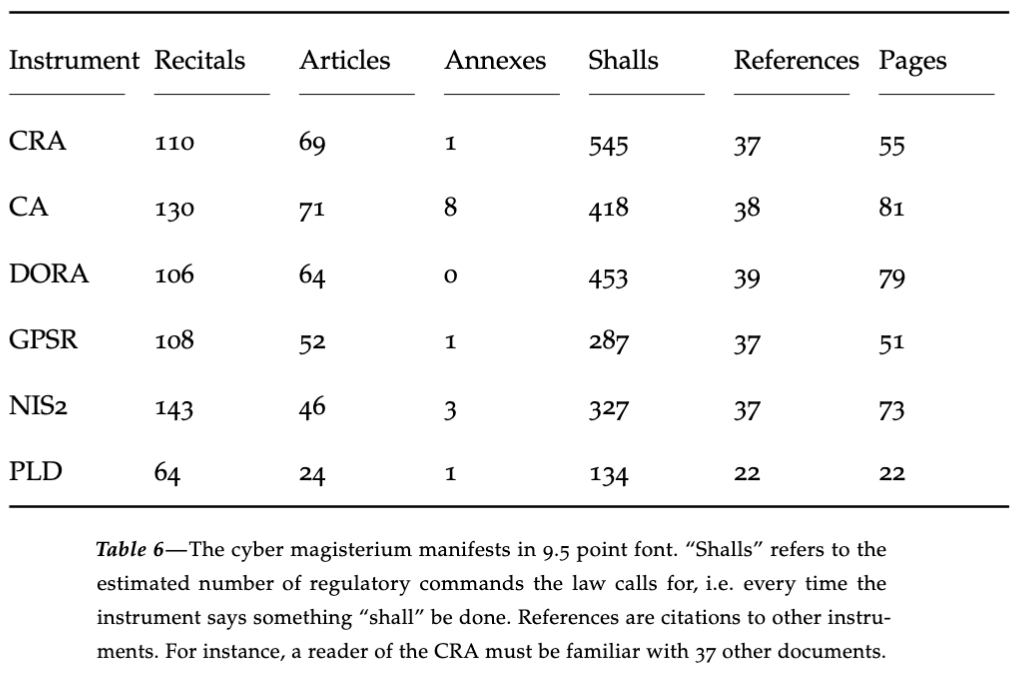
The EU Cybersecurity Framework: What it is, What it Means
If your clients develop standalone software or connected products, they need to know about the European Cybersecurity Framework. Enacted with little public attention, the Framework imposes far-reaching obligations on developers of standalone software and connected products. It establishes a stringent software product liability regime with rigorous security requirements and no meaningful small-business relief. In many…
-
Bearometer Methods Fall 2025
All, here are some methods updates on the Bearometer for Fall 2025. Our faculty changes, and so our N fluctuates. In September 2025, we added new faculty who have joined the campus this fall, and eliminated entries for those departed. Our N also decreases over time as faculty opt out of the Bearometer. When we…
-
Bearometer 9: Student Preparation
The Faculty Bearometer sent the following question on April 29, 2025 to 2,564 faculty senate members: Thinking about the students you teach, what portion of them are exceptionally prepared, adequately prepared, minimally prepared, or not at all prepared for the level of rigor you believe UC Berkeley coursework requires? 238 responded. The results are available at the link available to faculty.
-
Bearometer 8: Getting Reimbursed
On April 22, 2025, we distributed the following question to senate faculty (2567 members) via Qualtrics email contacts. 237 completed the survey. Results are available in the link circulated to senate faculty. Over the past 12 months, approximately how much have you personally spent on work-related expenses without getting fully reimbursed, because of policy rules…
-
Bearometer 7: External Criticisms
On April 16, 2025, we distributed the following question to senate faculty (2564 members) via Qualtrics email contacts. 291 completed the survey. Results are available in the link circulated to senate faculty. In the current environment where our university’s mode of operation is being openly challenged by powerful outside forces, do you believe that some…
-
Bearometer 6: Chancellor Vision
On April 8, 2025, we distributed the following question to senate faculty (2579 members) via Qualtrics email contacts. 155 completed the survey. Results are available in the link circulated to senate faculty. A new chancellor means a new vision for Berkeley. What are the most important issues the strategic planning process should address?
-
Bearometer 5: Free Speech Temperature
On April 1, 2025, we distributed the following question to senate faculty (2588 members) via Qualtrics email contacts. 335 completed the survey. Results are available in the link circulated to senate faculty. Are you concerned about retaliation when you speak, or is your speech chilled by any of the classes of people listed below?
-
Bearometer 4: Intercollegiate Athletics
On March 4, 2025, we distributed the following question to senate faculty (2635 members) via Qualtrics email contacts. 341 completed the survey. Results are available in the link sent to senate faculty members. What level of priority should Berkeley place on intercollegiate athletics?
-
Bearometer 3: SAT/ACT Testing
On February 20, 2025, we distributed the following question to senate faculty (2635 members) via Qualtrics email contacts. 430 completed the survey. Results are available at the link sent to senate faculty members. Should UC Berkeley go back to using standardized test scores (e.g. SAT or ACT) in undergraduate applications?
-
Bearometer 2: Union
On February 11, 2025, we distributed the following question to senate faculty (2635 members) via Qualtrics email contacts: “As the University prepares to renegotiate the graduate student union agreement, what is the most important insight you want negotiators to understand about how the current agreement impacts your teaching or research?” 179 responded. Results available by…