Chris Jay Hoofnagle is Professor of Law in Residence at the University of California, Berkeley, School of Law, where he teaches cybersecurity, programming for lawyers, and torts. He is affiliated faculty with the Simons Institute for the Theory of Computing and the Center for Security in Politics. In Spring 2024, Hoofnagle visitied King’s College Department of War Studies.
Hoofnagle’s new book with Golden G. Richard III is Cybersecurity in Context (Wiley forthcoming 2024). Previous works include Law and Policy for the Quantum Age (with Simson Garfinkel, 2022) and Federal Trade Commission Privacy Law and Policy (2016), both with Cambridge University Press.
An elected member of the American Law Institute, Hoofnagle is of counsel to Gunderson Dettmer LLP, a longtime advisor to Palantir Technologies, and a member of the National Academies Intelligence Science and Technology Experts Group (ISTEG).
With Professor Daniel Solove, Hoofnagle founded the Privacy Law Scholars Conference.

In-progress works
-
Military ML: Missing the Target
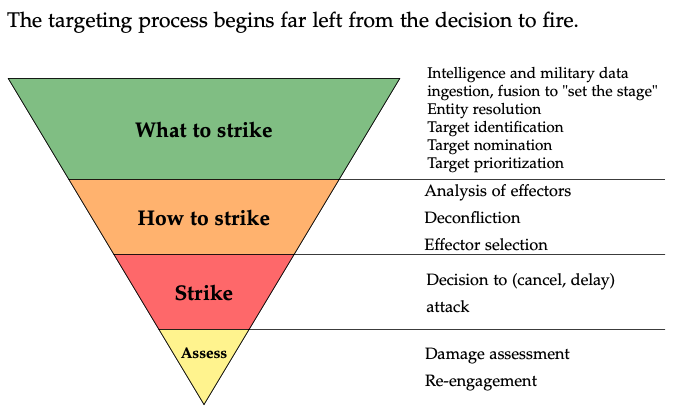
Are we on the precipice of developing autonomous killer robots; unmanned technologies that will completely dominate conflict, remorselessly, perfectly? Some advocates think so but this article explains why the killer robot view is misplaced and in its misdirection, draws attention away from how militaries are likely to use machine learning (ML) and artificial intelligence (AI)…
-
The Techcons
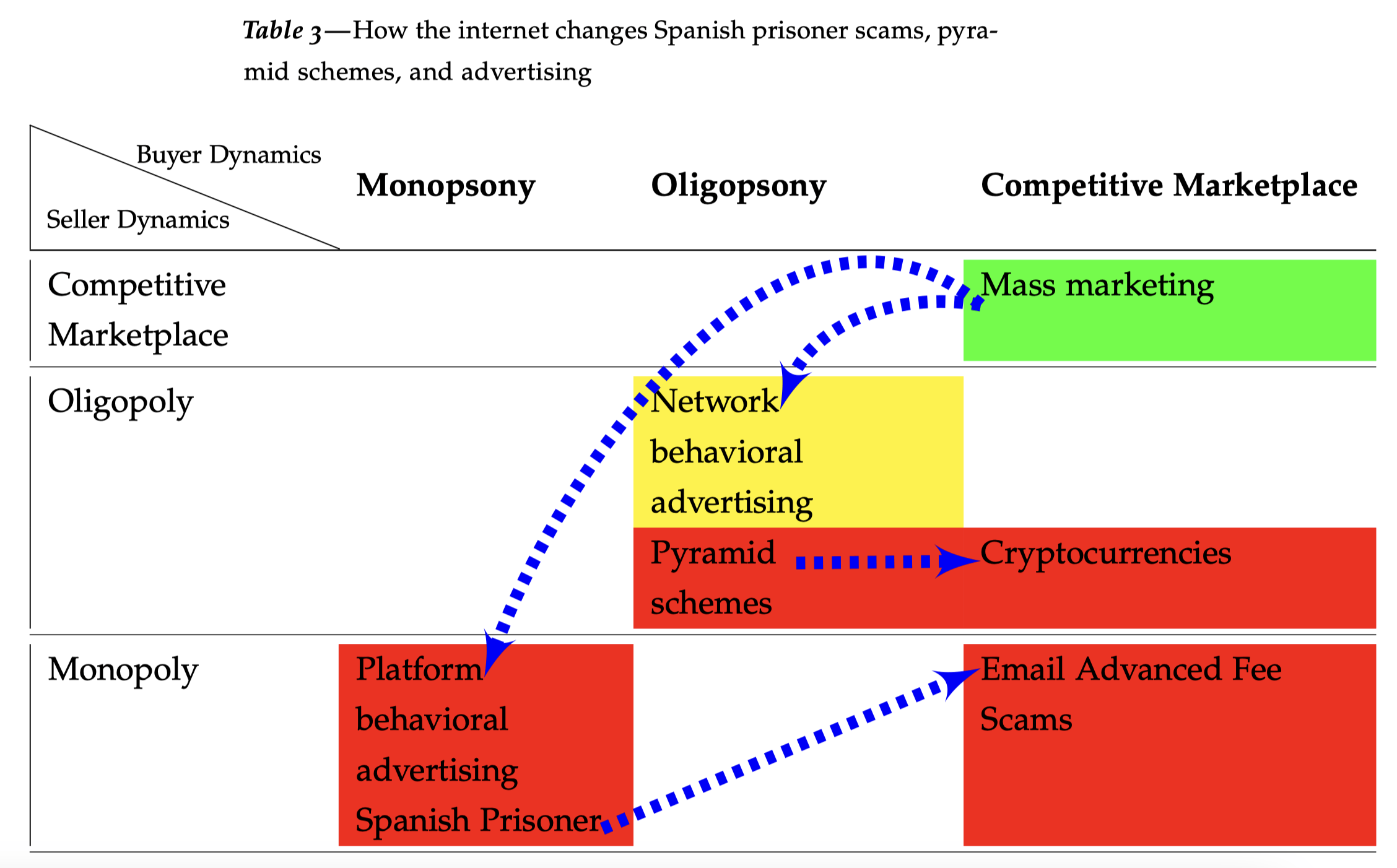
Revisiting Arthur Leff’s Swindling and Selling Yale Law Professor Arthur Leff wrote a powerful, market-structure analysis of consumer fraud in his 1976 Swindling and Selling. That work is more or less lost to history. Leff explained that con artists attempted to impose a false economy on marks. In a perfect congame, such as the Spanish Prisoner,…
-
What is consumer privacy?
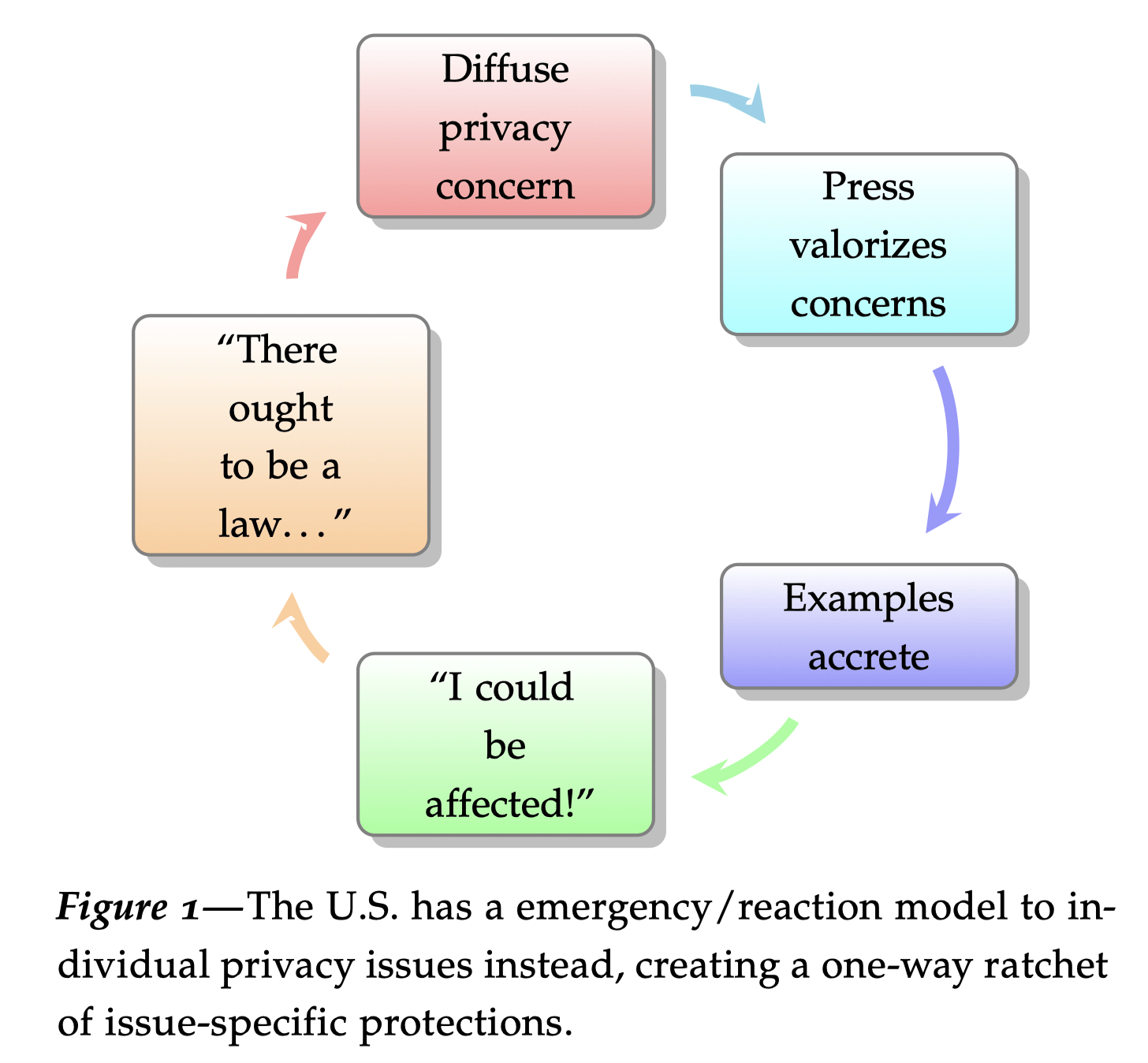
In this essay for a lecture at Stanford University, I attempt to explain consumer privacy as a deterrence theory strategy. I argue that privacy does have methods of analysis, based in fair information practices, while popular use of the term “privacy” is loose, a shibboleth representing uncertain values. This wide-ranging essay then goes on to…
Publications
h-index: 32, i10: 43
Turow, Joseph; Bleakley, Amy; Bracken, John; Carpini, Michael X Delli; Draper, Nora; Feldman, Lauren; Good, Nathaniel; Grossklags, Jens; Hennessy, Michael; Hoofnagle, Chris Jay; others,
Americans, Marketers, And The Internet: 1999-2012 Journal Article
In: SSRN 2423753, 2014.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@article{turow2014americans,
title = {Americans, Marketers, And The Internet: 1999-2012},
author = {Joseph Turow and Amy Bleakley and John Bracken and Michael X Delli Carpini and Nora Draper and Lauren Feldman and Nathaniel Good and Jens Grossklags and Michael Hennessy and Chris Jay Hoofnagle and others},
url = {https://repository.upenn.edu/entities/publication/eb45614c-a9f4-4248-b18b-1acb2653b5d2},
year = {2014},
date = {2014-01-01},
journal = {SSRN 2423753},
abstract = {This is a collection of the reports on the Annenberg national surveys that explored Americans' knowledge and opinions about the new digital-marketing world that was becoming part of their lives. So far we’ve released seven reports on the subject, in 1999, 2000, 2003, 2005, 2009, 2010, and 2012. The reports raised or deepened a range of provocative topics that have become part of public, policy, and industry discourse.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {article}
}
Hoofnagle, Chris Jay; Urban, Jennifer M
Alan Westin’s privacy homo economicus Journal Article
In: Wake Forest L. Rev, vol. 49, pp. 261, 2014.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@article{hoofnagle2014alan,
title = {Alan Westin's privacy homo economicus},
author = {Chris Jay Hoofnagle and Jennifer M Urban},
url = {https://heinonline.org/HOL/LandingPage?handle=hein.journals/wflr49&div=13&id=&page=},
year = {2014},
date = {2014-01-01},
journal = {Wake Forest L. Rev},
volume = {49},
pages = {261},
abstract = {Homo economicus reliably makes an appearance in regulatory debates concerning information privacy. Under the still-dominant U.S. “notice and choice” approach to consumer information privacy, the rational consumer is expected to negotiate for privacy protection by reading privacy policies and selecting services consistent with her preferences. A longstanding model for predicting these preferences is Professor Alan Westin's well-known segmentation of consumers into “privacy pragmatists,” “privacy fundamentalists,” and “privacy unconcerned.”
To be tenable as a protection for consumer interest, “notice and choice” requires homo economicus to be broadly reliable as a model. Consumers behaving according to the model will know what they want and how to get it in the marketplace, limiting regulatory approaches to information privacy. While notice and choice is undergoing strong theoretical, empirical, and political critique, U.S. Internet privacy law largely reflects these assumptions.
This Article contributes to the ongoing debate about notice and choice in two main ways. First, we consider the legacy Westin's privacy segmentation model itself, which as greatly influenced the development of the notice-and-choice regime. Second, we report on original survey research, collected over four years, exploring Americans’ knowledge, preferences, and attitudes about a wide variety of data practices in online and mobile markets. Using these methods, we engage in considered textual analysis, empirical testing, and critique of Westin’s segmentation model.
Our work both calls into question longstanding assumptions used by Westin and lends new insight into consumers’ privacy knowledge and preferences. A close textual look at factual and theoretical assumptions embedded in the segmentation model shows foundational flaws. With testing, we find that the segmentation model lacks validity in important dimensions. In analyzing data from nationwide, telephonic surveys of Internet and mobile phone users, we find an apparent knowledge gap among consumers concerning business practices and legal protections for privacy, calling into question Westin’s conclusion that a majority of consumers act pragmatically. We further find that those categorized as “privacy pragmatists” act differently from Westin’s model when directly presented with the value exchange — and thus the privacy tradeoff — offered with these services.
These findings reframe the privacy pragmatist and call her influential status in U.S. research, industry practice, and policy into serious question. Under the new view, she cannot be seen as “pragmatic” at all, but rather as a consumer making choices in the marketplace with substantial deficits in her understanding of business practices. This likewise calls into question policy decisions based on the segmentation model and its assumptions. We conclude that updated research and a policy approach that addresses both rationality and knowledge gaps are key.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {article}
}
To be tenable as a protection for consumer interest, “notice and choice” requires homo economicus to be broadly reliable as a model. Consumers behaving according to the model will know what they want and how to get it in the marketplace, limiting regulatory approaches to information privacy. While notice and choice is undergoing strong theoretical, empirical, and political critique, U.S. Internet privacy law largely reflects these assumptions.
This Article contributes to the ongoing debate about notice and choice in two main ways. First, we consider the legacy Westin’s privacy segmentation model itself, which as greatly influenced the development of the notice-and-choice regime. Second, we report on original survey research, collected over four years, exploring Americans’ knowledge, preferences, and attitudes about a wide variety of data practices in online and mobile markets. Using these methods, we engage in considered textual analysis, empirical testing, and critique of Westin’s segmentation model.
Our work both calls into question longstanding assumptions used by Westin and lends new insight into consumers’ privacy knowledge and preferences. A close textual look at factual and theoretical assumptions embedded in the segmentation model shows foundational flaws. With testing, we find that the segmentation model lacks validity in important dimensions. In analyzing data from nationwide, telephonic surveys of Internet and mobile phone users, we find an apparent knowledge gap among consumers concerning business practices and legal protections for privacy, calling into question Westin’s conclusion that a majority of consumers act pragmatically. We further find that those categorized as “privacy pragmatists” act differently from Westin’s model when directly presented with the value exchange — and thus the privacy tradeoff — offered with these services.
These findings reframe the privacy pragmatist and call her influential status in U.S. research, industry practice, and policy into serious question. Under the new view, she cannot be seen as “pragmatic” at all, but rather as a consumer making choices in the marketplace with substantial deficits in her understanding of business practices. This likewise calls into question policy decisions based on the segmentation model and its assumptions. We conclude that updated research and a policy approach that addresses both rationality and knowledge gaps are key.
Urban, Jennifer M; Hoofnagle, Chris Jay
The privacy pragmatic as privacy vulnerable Proceedings Article
In: Symposium on Usable Privacy and Security (SOUPS) 2014, July 9-11, 2014, Menlo Park, CA., 2014.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@inproceedings{urban2014privacy,
title = {The privacy pragmatic as privacy vulnerable},
author = {Jennifer M Urban and Chris Jay Hoofnagle},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=2514381},
year = {2014},
date = {2014-01-01},
booktitle = {Symposium on Usable Privacy and Security (SOUPS) 2014, July 9-11, 2014, Menlo Park, CA.},
abstract = {Alan Westin’s well-known and often-used privacy segmentation fails to describe privacy markets or consumer choices accurately. The segmentation divides survey respondents into “privacy fundamentalists,” “privacy pragmatists,” and the “privacy unconcerned.” It describes the average consumer as a “privacy pragmatist” who influences market offerings by weighing the costs and benefits of services and making choices consistent with his or her privacy preferences. Yet, Westin’s segmentation methods cannot establish that users are pragmatic in theory or in practice. Textual analysis reveals that the segmentation fails theoretically. Original survey data suggests that, in practice, most consumers are not aware of privacy rules and practices, and make decisions in the marketplace with a flawed, yet optimistic, perception of protections. Instead of acting as “privacy pragmatists,” consumers experience a marketplace myopia that causes them to believe that they need not engage in privacy analysis of products and services.
Westin’s work has been used to justify a regulatory system where the burden of taking action to protect privacy rests on the very individuals who think it is already protected strongly by law. Our findings begin to suggest reasons behind both the growth of some information-intensive marketplace activities and some prominent examples of consumer backlash.
Based on knowledge-testing and attitudinal survey work, we suggest that Westin’s approach actually segments two recognizable privacy groups: the “privacy resilient” and the “privacy vulnerable.” We then trace the contours of a more usable segmentation and consider whether privacy segmentations contribute usefully to political discourse on privacy.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {inproceedings}
}
Westin’s work has been used to justify a regulatory system where the burden of taking action to protect privacy rests on the very individuals who think it is already protected strongly by law. Our findings begin to suggest reasons behind both the growth of some information-intensive marketplace activities and some prominent examples of consumer backlash.
Based on knowledge-testing and attitudinal survey work, we suggest that Westin’s approach actually segments two recognizable privacy groups: the “privacy resilient” and the “privacy vulnerable.” We then trace the contours of a more usable segmentation and consider whether privacy segmentations contribute usefully to political discourse on privacy.
Urban, Jennifer M; Hoofnagle, Chris Jay; Li, Su
Mobile phones and privacy Technical Report
2012.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{urban2012mobile,
title = {Mobile phones and privacy},
author = {Jennifer M Urban and Chris Jay Hoofnagle and Su Li},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=2103405},
year = {2012},
date = {2012-01-01},
journal = {BCLT Research Paper Series},
abstract = {Mobile phones are a rich source of personal information about individuals. Both private and public sector actors seek to collect this information. Facebook, among other companies, recently ignited a controversy by collecting contact lists from users’ mobile phones via its mobile app. A recent Congressional investigation found that law enforcement agencies sought access to wireless phone records over one million times in 2011. As these developments receive greater attention in the media, a public policy debate has started concerning the collection and use of information by private and public actors.
To inform this debate and to better understand Americans’ attitudes towards privacy in data generated by or stored on mobile phones, we commissioned a nationwide, telephonic (both wireline and wireless) survey of 1,200 households focusing upon mobile privacy issues.
We found that Americans overwhelmingly consider information stored on their mobile phones to be private — at least as private as information stored on their home computers. They also overwhelmingly reject several types of data collection and use drawn from current business practices. Specifically, large majorities reject the collection of contact lists stored on the phone for the purposes of tailoring social network “friend” suggestions and providing coupons, the collection of location data for tailoring ads, and the use of wireless contact information for telemarketing, even where there is a business relationship between the consumer and merchant.
Respondents evinced strong support for substantial limitations on the retention of wireless phone usage data. Respondents also thought that some prior court oversight is appropriate when police seek to search a wireless phone when arresting an individual.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
To inform this debate and to better understand Americans’ attitudes towards privacy in data generated by or stored on mobile phones, we commissioned a nationwide, telephonic (both wireline and wireless) survey of 1,200 households focusing upon mobile privacy issues.
We found that Americans overwhelmingly consider information stored on their mobile phones to be private — at least as private as information stored on their home computers. They also overwhelmingly reject several types of data collection and use drawn from current business practices. Specifically, large majorities reject the collection of contact lists stored on the phone for the purposes of tailoring social network “friend” suggestions and providing coupons, the collection of location data for tailoring ads, and the use of wireless contact information for telemarketing, even where there is a business relationship between the consumer and merchant.
Respondents evinced strong support for substantial limitations on the retention of wireless phone usage data. Respondents also thought that some prior court oversight is appropriate when police seek to search a wireless phone when arresting an individual.
Hoofnagle, Chris Jay; Urban, Jennifer M; Li, Su
Privacy and Advertising Mail (Junk Mail) Technical Report
2012.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{hoofnagle2012privacymail,
title = {Privacy and Advertising Mail (Junk Mail)},
author = {Chris Jay Hoofnagle and Jennifer M Urban and Su Li},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=2183417},
year = {2012},
date = {2012-01-01},
journal = {SSRN},
abstract = {In this paper, we consider why Americans may frame the generation and receipt of unsolicited advertising mail as a privacy violation. We then present data from our nationwide survey showing that a very large majority of Americans, across all ideologies, educational attainment levels, age, and income levels, support the creation of a do-not-mail mechanism similar to the popular Telemarketing Do Not Call Registry. We discuss our results in light of the fact that direct advertising mail now makes up more than half of all mailpieces sent by the United States Postal Service (USPS).},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
Hoofnagle, Chris Jay; Urban, Jennifer M; Li, Su
Privacy and modern advertising: Most us Internet users want ‘do not track’ to stop collection of data about their online activities Technical Report
2012.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{hoofnagle2012privacy,
title = {Privacy and modern advertising: Most us Internet users want 'do not track' to stop collection of data about their online activities},
author = {Chris Jay Hoofnagle and Jennifer M Urban and Su Li},
url = {https://ssrn.com/abstract=2152135},
year = {2012},
date = {2012-01-01},
journal = {SSRN},
abstract = {Most Americans have not heard of 'Do Not Track,' a proposal to allow Internet users to exercise more control over online advertising. However, when probed, most prefer that Do Not Track block advertisers from collecting data about their online activities. This is a much more privacy-protective approach for Do Not Track than what has been proposed by the advertising industry.
In previous studies, we have found that Americans think they are protected by strong online privacy laws. Here, we probed beliefs about tracking on medical websites and 'free' websites, with most not able to answer true/false questions correctly about tracking. This result brings into question notice-and-choice models that depend on consumer understanding of the terms for their legitimacy.
We also probed Internet users' attitudes towards advertising. Most Internet users say that they do not find utility in online advertising, with half claiming that they never click on ads.
Advertisers and consumers are at an impasse on privacy. Advertisers seem to be seeking a kind of total information awareness for behavioral advertising, and have proposed self-regulatory guidelines with little bite. At the same time, both our survey evidence and media reports show consumer opposition to tracking.
Do Not Track has emerged from the current skirmish between consumers and advertisers, but it is a relatively modest intervention that does little to shift the underlying incentives that have driven increasing tracking and aggregation of information about consumers. It is foreseeable that regardless of the form Do Not Track takes, websites will simply require consumers to disable it in order to access content. A fundamental change in incentives may be necessary to relieve this impasse and find an approach for advertising that is not so dependent upon third-party tracking and aggregation of information, both online and off.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
In previous studies, we have found that Americans think they are protected by strong online privacy laws. Here, we probed beliefs about tracking on medical websites and ‘free’ websites, with most not able to answer true/false questions correctly about tracking. This result brings into question notice-and-choice models that depend on consumer understanding of the terms for their legitimacy.
We also probed Internet users’ attitudes towards advertising. Most Internet users say that they do not find utility in online advertising, with half claiming that they never click on ads.
Advertisers and consumers are at an impasse on privacy. Advertisers seem to be seeking a kind of total information awareness for behavioral advertising, and have proposed self-regulatory guidelines with little bite. At the same time, both our survey evidence and media reports show consumer opposition to tracking.
Do Not Track has emerged from the current skirmish between consumers and advertisers, but it is a relatively modest intervention that does little to shift the underlying incentives that have driven increasing tracking and aggregation of information about consumers. It is foreseeable that regardless of the form Do Not Track takes, websites will simply require consumers to disable it in order to access content. A fundamental change in incentives may be necessary to relieve this impasse and find an approach for advertising that is not so dependent upon third-party tracking and aggregation of information, both online and off.
Hoofnagle, Chris Jay; King, Jennifer; Li, Su; Turow, Joseph
How different are young adults from older adults when it comes to information privacy attitudes and policies? Technical Report
2010.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{hoofnagle2010different,
title = {How different are young adults from older adults when it comes to information privacy attitudes and policies?},
author = {Chris Jay Hoofnagle and Jennifer King and Su Li and Joseph Turow},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=1589864},
year = {2010},
date = {2010-01-01},
journal = {Available at SSRN 1589864},
abstract = {Media reports teem with stories of young people posting salacious photos online, writing about alcohol-fueled misdeeds on social networking sites, and publicizing other ill-considered escapades that may haunt them in the future. These anecdotes are interpreted as representing a generation-wide shift in attitude toward information privacy. Many commentators therefore claim that young people “are less concerned with maintaining privacy than older people are.” Surprisingly, though, few empirical investigations have explored the privacy attitudes of young adults. This report is among the first quantitative studies evaluating young adults’ attitudes. It demonstrates that the picture is more nuanced than portrayed in the popular media.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
Turow, Joseph; King, Jennifer; Hoofnagle, Chris Jay; Bleakley, Amy; Hennessy, Michael
Americans reject tailored advertising and three activities that enable it Technical Report
2009.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{turow2009americans,
title = {Americans reject tailored advertising and three activities that enable it},
author = {Joseph Turow and Jennifer King and Chris Jay Hoofnagle and Amy Bleakley and Michael Hennessy},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=1478214},
year = {2009},
date = {2009-01-01},
journal = {Available at SSRN 1478214},
abstract = {This nationally representative telephone (wire-line and cell phone) survey explores Americans' opinions about behavioral targeting by marketers, a controversial issue currently before government policymakers. Behavioral targeting involves two types of activities: following users' actions and then tailoring advertisements for the users based on those actions. While privacy advocates have lambasted behavioral targeting for tracking and labeling people in ways they do not know or understand, marketers have defended the practice by insisting it gives Americans what they want: advertisements and other forms of content that are as relevant to their lives as possible.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
King, Jennifer; Hoofnagle, Chris Jay
Wireless Location Privacy: Californians’ Awareness and Attitudes Towards Wireless Location Tracking Proceedings Article
In: Telecommunications Policy Research Conference, 2008.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@inproceedings{king2008wireless,
title = {Wireless Location Privacy: Californians' Awareness and Attitudes Towards Wireless Location Tracking},
author = {Jennifer King and Chris Jay Hoofnagle},
url = {https://www.law.berkeley.edu/files/gbo_location20072.pdf},
year = {2008},
date = {2008-01-01},
booktitle = {Telecommunications Policy Research Conference},
abstract = {While law enforcement increasingly locates individuals by gaining access to wireless phone records, a supermajority of Californians supports judicial intervention and informing suspects before law enforcement acquires retrospective (historical) location data on individuals from wireless phone companies. A majority of Californians understands that wireless phones can track their location, and that there is broad support for location tracking in emergency situations. When compared with Professor Alan Westin’s three privacy segments, “Fundamentalists,” “Pragmatists,” and the “Unconcerned,” Californians are more likely to be privacy pragmatists or fundamentalists, and less likely to be unconcerned about privacy. Generally, Westin's segmentation was not predictive of Californians' attitudes towards law enforcement access to wireless location data.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {inproceedings}
}
Hoofnagle, Chris Jay; King, Jennifer
What Californians understand about privacy online Technical Report
2008.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{hoofnagle2008research,
title = {What Californians understand about privacy online},
author = {Chris Jay Hoofnagle and Jennifer King},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=1262130},
year = {2008},
date = {2008-01-01},
journal = {SSRN 1133075},
abstract = {In order to gauge Californians' understanding of privacy policies and default rules in the online environment, we commissioned a representative survey of adults in the State (N=991). The telephonic survey of Spanish and English speakers was conducted by the Survey Research Center of University of California, Berkeley.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
Hoofnagle, Chris Jay; King, Jennifer
What Californians understand about privacy offline Technical Report
2008.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{hoofnagle2008californians,
title = {What Californians understand about privacy offline},
author = {Chris Jay Hoofnagle and Jennifer King},
url = {https://papers.ssrn.com/sol3/papers.cfm?abstract_id=1133075},
year = {2008},
date = {2008-01-01},
journal = {Available at SSRN},
abstract = {Many online privacy problems are rooted in the offline world, where businesses are free to sell consumers' personal information unless they voluntarily agree not to or where a specific law prohibits the practice. In order to gauge Californians' understanding of business practices with respect to the selling of customer data, we asked a representative sample of Californians about the default rules for protecting personal information in nine contexts. In six of those contexts (pizza delivery, donations to charities, product warranties, product rebates, phone numbers collected at the register, and catalog sales), a majority either didn't know or falsely believed that opt-in rules protected their personal information from being sold to others. In one context - grocery store club cards - a majority did not know or thought information could be sold when California law prohibited the sale. Only in two contexts - newspaper and magazine subscriptions and sweepstakes competitions - did our sample of Californians understand that personal information collected by a company could be sold to others.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
Turow, Joseph; Mulligan, Deirdre K; Hoofnagle, Chris Jay
Consumers Fundamentally Misunderstand the Online Advertising Marketplace Technical Report
2007.
Abstract | Links | BibTeX | Tags: Privacy, Public Opinion
@techreport{turow2007consumers,
title = {Consumers Fundamentally Misunderstand the Online Advertising Marketplace},
author = {Joseph Turow and Deirdre K Mulligan and Chris Jay Hoofnagle},
url = {https://www.law.berkeley.edu/files/annenberg_samuelson_advertising.pdf},
year = {2007},
date = {2007-01-01},
journal = {Research Report},
abstract = {Surveys of the public conducted by academic researchers at the University of Pennsylvania Annenberg School for Communication and UC-Berkeley Law’s Samuelson Law, Technology & Public Policy Clinic indicate that when consumers see the term “privacy policy,” they assume the website cannot engage in many practices that, in reality, are common in ecommerce. Consumers do not understand the nature and legality of information-collection techniques that form the core of online advertising business models. When these techniques and the business model of online advertising are explained to them, they reject the privacy tradeoff made for access to content.},
keywords = {Privacy, Public Opinion},
pubstate = {published},
tppubtype = {techreport}
}
For a list of research organized by research theme/question, click here.
Teaching
-
Cybersecurity in Context
New course: Fall 2024! In fall 2024, I will teach Cybersecurity in Context in the Legal Studies program (LS 190). The course will be based on my new textbook with Golden G. Richard III. Course Description Cybersecurity has become instrumental to economic activity and human rights alike. But as digital technologies penetrate almost every aspect…
-
Cybersecurity Courses @ Cal
A growing number of faculty are offering cybersecurity courses at Cal. Consider taking: The Center for Security in Politics offers a graduate certificate in security policy. Many of the electives are open to undergraduates. They include GSPP PP 155/255 Introduction to Security Policy (Professors Janet Napolitano and Daniel Sargent) PPC285 and NUCENG 285C Nuclear Security: The…
-
Computer Programming for Lawyers

Most recent syllabus: Spring 2023. Clients increasingly want their lawyers to understand their products and services on a technical level. Regulators need to understand how their rules will be implemented in code. Lawyers increasingly need tools to automate the process of collecting, organizing, and making sense of impossibly large troves of information. Computer Programming for…
-
Torts (1L)
Welcome to your first year of law school and to torts, a topic as rich as it is traditional in legal education. Torts provides an expansive lens to learn about the American legal system. This course will cover the basics of torts and in the process, the fundamental reasons and principles underlying doctrine. Learning Goals:…
-
Cybersecurity Working Group
We will discuss cybersecurity policy among a group of graduate, professional, and undergraduate students. The FCWG will be led by Andrew Reddie in Fall 2023 and Spring 2024. Chris Hoofnagle will lead it in Spring 2025 Previous syllabi (Fall 2023, Spring 2023, Fall 2022, Fall 2021, Spring 2021, Spring 2020, Spring 2019, Spring 2018, Fall 2017, Spring 2017)
-
Technology for Lawyers Workshop (TLW)

Technology for Lawyers Workshop (TLW) is a self-paced, two-session workshop covering the computer skills most important to success in law school. By working along and doing the exercises, you’ll become a more efficient user of your computer, and in the process, develop Microsoft Word templates you can use for law school assignments. Anyone in the…
-
Inactive Courses
Privacy Law for Technologists Information privacy law profoundly shapes how internet-enabled services may work. Privacy Law for Technologists will translate the regulatory demands flowing from the growing field of privacy, information security, and consumer law to those who are creating interesting and transformative internet-enabled services. The course will meet twice a week, with the first…
Governance
Berkeley has big problems with governance. I have a hypothesis of what has gone wrong and what to do about it.
-
What is the Faculty Bearometer
The Faculty Bearometer is a one-question survey posed to the Senate Faculty on issues of teaching and governance. Read more about it here.
-
What is the Faculty Budget Forum (FBF)?
The Faculty Budget Forum is Berkeley largest email list for faculty-to-faculty interaction on governance matters.
-
Fundamental Challenge: Strategy
Understanding our terminal goals is the core challenge of governance. Our terminal goals are to have world-class research and excellent teaching. Our governance activities should focus on promoting these strategic goals, and limiting the effects of other goals on these strategic goals. It’s easier for me to get reimbursed by stodgy European universities, where I…
-
Proposed Principles for Policy Evaluation
All senate committees should consider this framework for policy analysis.
-
Questions for the Vice Chancellor for Administration
In my opinion, some of Berkeley’s biggest problems emerge from the VCA’s portfolio.
-
On Administrative Misalignment
This is my diagnosis of Berkeley’s ills: a problem I call administrative misalignment. Some administrators are not working for Berkeley; they are working for something else. Maybe themselves.
-
Comments on “Sustainability”
Comments on the Proposed Presidential Policy on Sustainable Practices Thank you for inviting comment on the Proposed Presidential Policy on Sustainable Practices (“Policy”). While well-intended, the Policy creates numerous requirements untethered from our terminal goals of excellence in research and teaching. The Policy will require effort from many staff and consultants while not improving teaching…
FAQs
What is TLW—the Technology for Lawyers Workshop?
Technology for Lawyers Workshop (TLW) is a self-paced, two-session workshop covering the computer skills most important to success in law school.
By working along and doing the exercises, you’ll become a more efficient user of your computer, and in the process, develop templates you can use for law school assignments.
Session 1 is 40 minutes long, and it focuses on your computer generally and clever uses of the Web.
Session 2 is a deep dive into Microsoft Word. In this session, you will learn how to make proper templates for your legal writing. The session is 90 minutes long.
You can self-enroll here: https://bcourses.berkeley.edu/enroll/YCXH8X
Will you serve on my quals or PhD committee?
Maybe! I am a senate member and member of both the law and information faculties, so I can serve as an outside member in many configurations. Please email me a description of your research agenda, and how you think my participation will benefit your research.
I will not pay attention to a QE or other proceeding on Zoom. Sorry.
I’ve heard about your plantar fasciitis tricks…
Yes, plantar fasciitis is super annoying. Years ago, I found a literature review (can’t find it anymore) that suggested that all interventions for plantar fasciitis were equally inefficacious, and it is a condition that takes about 18 months to heal. Ouch! Furthermore, my foot doctor told me that surgery alleviates the pain but undermines the strength of your foot.
But I discovered a few tricks:
- These boots that one wears overnight to keep your foot tensioned work quickly to alleviate acute pain. Don’t use the sock ones. Use the full size one that looks like a plastic cast for a broken foot. Don’t over tighten it. Just use it so that your foot is angled slightly more than 90 degrees. If you can’t sleep with it, the boot is probably too tight or too aggressively angled.
- Voltaren, a “arthritis pain reliever,” now available over the counter-generic as diclofenac gel, is a godsend. They key is that you can put it on your foot and avoid the digestive complications from oral anti-inflammatories. Voltaren got me running in less than a week.
- Some sports, because of how your foot is angled, do not aggravate the plantar fascia. For instance, downhill skiing is great—your foot is stretched by the ski boot, making it almost like an hours-long treatment. Similarly ice skating does not aggravate my fascia even if done for hours. So you can keep in shape.
- I’ve found that the elliptical trainer doesn’t aggravate plantar fascia, and so you can do it for hours without injury. Don’t buy a cheap elliptical, they’re junk. Don’t trust the reviews either. You need to spend over $1k. The Sole E35 is a solid choice. But my favorite elliptical is the Octane XT and Q series standing ellipticals, which have stride lengths over 20 inches. You can find them on Craig’s List. I bought one used from a commercial gym for about $1k.
- Watch out for watches! I got a new Garmin watch, and it nudged me to run long and longer. I found myself running 10ks every other day, and then ended up with plantar again, putting me back at 2 mile runs…
Don’t overdo it. When I feel pressure in my heel, I know I am close to injuring my plantar fascia. So, for me at least, this is a permanent running injury
How do you contribute to DEI at Berkeley?
Technology law as a field is not known as being particularly diverse, nor inclusive. In my career at Berkeley, I have taken specific, sustained action to promote women in higher education, to raise awareness of SES issues in technology, and to include underrepresented and minority students in my work. Come by my office hours and I can speak with you in greater detail about these efforts. I’d also love to hear your thoughts about how BCLT can address systemic inequalities.
Recent events have caused me to deepen diversity and inclusion efforts in teaching. I plan to devote more classroom time to the structural causes of exclusion and inequality. For instance, in my technology courses generally, I intend to connect students with the history of Silicon Valley, and the root causes that made the area and its most successful companies homogenous. Few people know that Lockheed was the largest employer in the Valley until the rise of the .com bubble. Lockheed and other defense industrial base companies were male and white dominant (Lockheed was 85% male and 90% white even after equal opportunity laws were enacted). The demands of secrecy surrounding the DIB, the military R&D subject matter, and other factors caused systematic exclusion since the 1940s. Thus, when we think about inclusion in tech today, we have to contemplate addressing decades of disadvantage.
Confronting inequality is also a key element in my pure doctrinal courses, such as torts. I use the Witt/Tani casebook because it starts by situating the institutions of torts, because it explains how key doctrines compensate women and minorities and the poor differently, and because many of the cases selected by Witt and Tani have clear social class or race dynamics. Traditional cases that never received a class analysis—from Vosburg to Palsgraf—are recast in their casebook. My aim is to arm students with these insights so they can critically discuss the tradeoffs and implications of legal policies that promote formal equality or substantive equity.
Where can I find Berkeley Old Style Fonts?
What is the Faculty Budget Forum (FBF)?
The Faculty Budget Forum (FBF) is an email list of about 400 Berkeley faculty members. It is among the largest lateral (department to department) lists we have—the other being Teach-Net. If you are a faculty member, I am happy to add you to FBF. Just email me.
Will you supervise my JSP or JSD (PhD in law)?
Maybe! It is a delight to have a multi-year collaboration with JSP and JSD students. But JSP and JSD degrees require serious commitment because the point is not just for you to learn, but for you to make a new contribution to the literature. When you write your purpose statement, it’s not enough to just identify a topic. You must drill down and identify:
- The intellectual ideas that you want to engage in
- The literature surrounding your proposal, and how your investigation will answer problems not yet explored adequately
- Ideas that are “big enough” to justify a multi-year exploration
- Ideas that are important enough to justify the exploration—after all, you are going to spend years of your life on it
- The reasons why Berkeley is the right place for this exploration (what faculty/departmental/institutional characteristics of Berkeley are a good match for you)
- The training/experience you have that will make you successful in the research journey
Whom have you mentored at Berkeley?
Despite teaching in a professional program, I’ve had the chance to mentor some graduate students, including:
- Shazeda Ahmed, Berkeley PhD
- Zehra Betul Ayranci, Berkeley PhD, Fox Sports
- James Carney, Joanne Jia, Archana Kulkarni, Cameron Lopez, PrivacyBot Capstone Project (Information)
- Ella Corren, JSP
- Amit Elazari Bar On, head of global cybersecurity, Intel
- Gal Forer, JSD
- Kevin Frazier, USD Law
- Alexi Pfeffer-Gillett, UMD Law
- Grace Gordon, Master of Development Practice
- Arianne Jimenez, Privacy and Public Policy Manager Facebook APAC
- Aniket Kesari, Yale/Berkeley JD/PhD, Fordham Law
- Irene Kamara, Standardising data protection: a European perspective in an interconnected world, Tilburg University (Netherlands)
- Sam Kumkar, EECS
- Morgan Livingston, ISF
- Sylvia Lu, Law
- Rachna Mandalam, ISF
- Nicole van der Meulen, EC3
- Andrew Reddie, UC Berkeley
- Nikita Samarin, EECS
- Ankeet Shankar, Capstone Project (Information)
- Bart van der Sloot, Tilburg University
- Ashkan Soltani, privacy/security researcher
- Eric Winkofsky, JSD
In addition to these students, with Dean Shankar Sastry, I was Co-PI of a program (TRUST SITE REU) with a goal to increase diversity in graduate STEM programs. We hosted scores of undergraduates at Cal, and in some cases, I published papers with these students, including Mika Ayenson (Johns Hopkins University Applied Physics Laboratory), Shannon Canty, Quentin Mayo, and Lauren Thomas.
I’m a prospective student, will you…?
Apologies, I generally do not meet with students unless they are admitted to a program. Similarly, if you are a student at another program, apologies, I cannot supervise or give you advice on your research.
Please know that admissions at Berkeley is handled by a committee and that I have no influence over decisions.
What is your role with the academic senate?
I ran for the UCB Divisional Council in 2022 and won election for the 22-23, and 23-24 years. Known as DIVCO, the body could be thought of as the executive arm of Berkeley’s academic senate. I ran because of concerns about campus priorities and the strategic challenges we face. Berkeley is facing macro constraints including costs of housing and living in the Bay Area that are steadily eroding our competitive posture, and at the same time we lack features that help institutions perform (biggest example: no medical school).
We should be thinking big, with eyes on a 2030–2040 horizon. Some of the ideas I think are worth pursuing include: creating faculty housing like that offered at NYU and Colombia, creating student housing close to campus—even using eminent domain to reform the sleepy properties that surround the campus, rethinking how much of our central campus is devoted to sports infrastructure, building a medical school, and developing campus institutions that can more competitively interact with D/I/H-ARPA.
We should fundamentally rethink how we can use campus resources to compete for and retain faculty. Other schools use campus resources to provide perks for faculty that we simply don’t consider. For instance, we have a fantastic eye clinic at Berkeley—why won’t we offer corrective vision surgery as a retention strategy, or as a privilege connected with earning tenure, or even as a recruitment tool for the best graduate students?
I also ran because in my opinion, Berkeley gets in its own way too often. We literally decide not to do “the right thing” or the strategic thing because of transaction costs we have imposed upon ourselves. We are becoming more process-based and managerial. Just as employees adopt “shadow-IT” to circumvent bad technology decisions, some faculty employ shadow-operations to get their work done.
Senior faculty members spend much of their time now on process and paperwork. We need to formally declare a time-value to faculty member time, and eliminate rules, trainings, and paperwork that 1) excessively impose upon faculty time or 2) are not risk-justified. From reimbursements to CPHS to IACUC to even the merit review process, we have no evaluative method that acts as a ceiling on paperwork and faculty time and we don’t probe the upside/downside risks from process requirements.
Candidate Statement
My governance experience at Cal includes campus-level (CPHS, leading the Center for Long Term Cybersecurity, developing a professional masters in cybersecurity, Senate academic freedom committee) and school-level service (HGA of our cyber program, building space, admissions). I am a former member of the AAUP’s Committee A on Academic Freedom and Tenure and helped it develop policy on protection of electronic communications. I am also a practicing attorney and advisor to companies operating high-risk, high-consequence activities. I have raised money from NSF, from many companies, and I led a grant-making foundation.
My governance philosophy is guided by several high-level principles and concerns: our institution’s competitive posture; a structural perspective on campus challenges (I believe it is important to avoid using policies that impose costs on individuals when the problem being addressed is systemic in nature); the need to protect faculty time and attention from growing compliance, training, and other administrative obligations; and my sense that as an institution, we are becoming too risk adverse.
As a dual appointee in two professional schools (Law & Information), I have worked with many colleagues in the humanities and sciences. One of my goals has been to increase lateral faculty information sharing, and to that end I have helped moderate the Faculty Budget Forum. As a member of DIVCO, I would endeavor to help others understand and contribute to the complex governance landscape of our wonderful campus.
What conflicts of interest do you have?
The University of California recognizes that engagements in the private sector enrich academics’ research and teaching. I teach at professional schools, which tend to encourage teaching and research related to practice challenges. There’s a tradeoff between private sector engagements and benefits to students. For instance, several of my classes are based on client scenarios and my writing is informed by real business needs and constraints.
Norms surrounding conflicts disclosure and regulation is highly disciplinary. In some fields, experts think themselves above conflicts and do not disclose them. In others, such as law, norms of client confidentiality cause some academics to keep their conflicts secret. And some universities allow study sponsors to control the outcomes of research—something that is explicitly prohibited at Cal.
I serve on boards to two companies, Constella Intelligence (cybersecurity intelligence) and Palantir Technologies. I have also served on the boards of non-profits and operated a foundation, but no one seems concerned about those conflicts, and if you ask me in person, I’ll explain why you should be 
My work has been directly or indirectly supported by many technology companies, including Apple, Google, Microsoft, Palantir, and Nokia. I always disclose specific sponsors of my research projects, and all situations where my academic work may be colored by a client or sponsor.
What is the Privacy Law Scholars Conference (PLSC)?
With Dan Solove, I started the Privacy Law Scholars Conference in 2008 (PLSC). The PLSC is a paper workshop for in-progress scholarship related to information privacy. The conference was based on the well-established Intellectual Property Law Scholars Conference and some ideas we borrowed from other conference: long networking breaks, all conversations, an emphasis on collegial and helpful interactions, and no panels. We also adopted the practice of having papers presented by a “commenter”—a designated discussion leader who introduced the paper and then curated the conversation amongst the group. This last innovation is key. It creates a lively dynamic where you don’t have the author droning on and on. It also helps the author understand what the reader actually learned from the paper. Many of the most important articles in the privacy law field were workshopped at PLSC.
I am no longer involved in PLSC, but am proud of what it has become, and am delighted that the model has been deployed elsewhere. There are now PLSCs in Europe, Latin America, and even regional mini-PLSCs in the US.
I am an undergrad/grad, may I take your course?
Probably yes.
Graduate students, you can enroll if my course has a non-Law prefix, such as Info.
Undergraduate students, you can enroll in INFO and Legal Studies (but not LAW) courses with permission. To obtain permission, email me the following information. I typically enroll undergraduates after the graduate registration period.
1. I am an upper-division student [Yes/No]
2. What year?
3. I understand and accept that this is a graduate-level class, with graduate-level materials and pacing. [Yes/No]
4. I understand and accept that participation in class discussion is expected, even if the class is larger than most undergraduate courses that expect this (in grad and law school classes, for example, students participate in discussion in 50-100-person classes). [Yes/No]
5. I would like to take this class because: [Please tell us why you would like to take the class.]
6. I would contribute to this class because: [Please tell us why you would contribute to the class. For example, your major is relevant to topics in the class; you are doing an undergrad thesis on a relevant topic; you worked on relevant issues prior to coming to Berkeley; etc.]
Will you write me a letter of recommendation?
Probably yes 
First, faculty need time. A month before the deadline is great.
Second, could you send me the following information:
- The position title and submission information.
- Information about the position
- Your resume or CV
- A short description of your long-term career goals
- In your own words, why you think you are a good fit for the opportunity
- In your own words, why you think the opportunity is a good one
Where can I find your LaTeX templates?
Check out my Github for:
Old school Berkeley letterhead
The 2020 Berkeley formal letterhead
The 2020 Berkeley casual letterhead
What is your AI-compliant email auto-responder message?
Pursuant to Article 52 of the EU AI Act, please be aware that this message comes from a low-risk “AI” system and not a human. All AI systems pose risks, including but not limited to spreading misinformation, causing emotional manipulation, engaging in invidious discrimination, the mis-operation of lethal autonomous weapons systems, the erosion of all human responsibility for decision-making and good judgment, the rendering useless of humanity, and/or a mass extinction event from misaligned superintelligence. Any information produced by this system must be processed with the highest caution. The University of California disclaims any claims or disclaimers made by this system. Do not rely on any information conveyed here without verifying it. You have no rights under Article 22 of the GDPR to object to this system, because sending email to this address is explicit consent to automated processing, including profiling. This system is not pre-registered in China; emails received from this system in China are hereby recalled.
